Java + SSL + Keystore = Royal PITA
I just spent all morning reading and trying things from every SSL guide and support ticket on these forums and got nowhere.
I’ve finally figured out and documented the steps that actually work to get a signed SSL certificate installed on Openfire.
Note: Java’s keytool DOES NOT WORK for importing Openfire’s keystore!
- Set Openfire’s keystore to JKS mode:
xmpp.socket.ssl.keystore =/usr/share/openfire/resources/security/keystore
xmpp.socket.ssl.storeType = JKS
- Convert yourdomain.net.au cert to pkcs12 with private key:
openssl pkcs12 -export -in yourdomain.net.au.crt -inkey yourdomain.net.au.key -out yourdomain.net.au.key.pkcs12 -name yourdomain.net.au
- Copy pkcs12 to workstation and install keystore-explorer
http://keystore-explorer.sourceforge.net
-
Create a new JKS KeyStore in keystore-explorer
-
Import pkcs12 to keystore-explorer
-
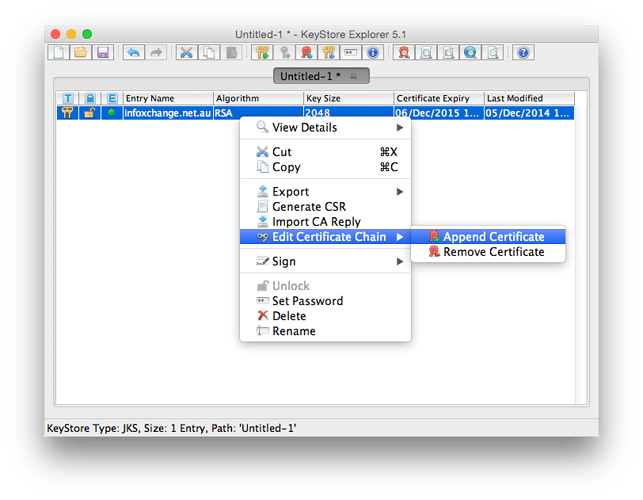
Append to cert chain all other upstream certs in zip file from your ssl provider
-
Save the keystore with changeit as keystore password
-
Copy keystore back to Openfire
scp keystore root@int-jabber-01:/usr/share/openfire/resources/security/keystore
- Fix permissions
chmod 644 /usr/share/openfire/resources/security/keystore
chown openfire:openfire /usr/share/openfire/resources/security/keystore
- Restart Openfire
service openfire restart
2 Likes
You can skip the conversion to PKCS#12. KeyStore Explorer can directly import .crt and .key files, just select PKCS#8 as key type.
Also, here is my direct cli approach with (debian) script:
Cheers!
Christian, your alpha-labs link throws a SSL Certificate Error for me. Could you copy-paste the instructions here? Or post a new How-to?
This doesnt work for me. I don’t know why.
After i have step for step done the HowTo Openfire wrote: One or more certificates are missing. Click here to generate self-signed certificates or here to import a signed certificate and its private key.
Actually you’re all done. You only need the one imported certificate. The missing certificate is a DSA certificate that’s not needed nowadays. You should have a valid and working RSA certificate, tho.
Well,
time to upgrade your browser If it can’t visit that site, then your browser does not support high-grade encryption with DH exchange. Anyway, I copy&pasted the stuff here: https://edit.alpha-labs.net/p/7zD6BfcAld which should look terrible, If you cant visit that server, too – well, really do upgrade your browser.
For a list of required ciphers for that server (and many, many more) see this page: https://www.ssllabs.com/ssltest/analyze.html?d=alpha-labs.net
Cheers!
I am not sure if it will help you but in “import” screen, dont leave Pass Phrase empty even though you are not using it. Just type “ABC” or “123”. Then use insert private key in “Content of Private Key file:”. In “Content of Certificate file:” section, enter content of your certificate followed up intermediate certificate chain. In the GoDaddy version (we used), it is certificate + gd_bundle.crt. In GoDaddy, you might receive ssl certificate in tomcat, apache, IIS version. Use tomcat version for this.
Also before importing this cert, please make sure that gd_bundle.crt is imported in truststore. Use following command to import them,
sudo keytool -import -trustcacerts -keystore truststore -alias com_godaddy_certificates -file gd_bundle.crt
Openfire truststore is located in …/openfire/resources/security folder so you have to enter above command in that directory. Please restart the server if after executing command and then import SSL certificate.
It must be something with OS X.
I’m running OS X Yosemite with the latest versions of Safari, Firefox, and Chrome. Results:
Chrome:
Both https://alpha-labs.net/2014/12/openfire-and-ciphers/ and https://edit.alpha-labs.net/p/7zD6BfcAld
https://edit.alpha-labs.net/p/7zD6BfcAld give “Your connection is not private, NET: ERR_CERT_INVALID”
Safari
Both https://alpha-labs.net/2014/12/openfire-and-ciphers/ and https://edit.alpha-labs.net/p/7zD6BfcAld
hang indefinitely
Firefox
https://alpha-labs.net/2014/12/openfire-and-ciphers/ gives 400 Bad Request
https://edit.alpha-labs.net/p/7zD6BfcAld actually works!
So, you are 1/6 here running some of the most commonly used browsers. Can’t test Internet Explorer because … OS X.
I tried on a Windows 7 machine and it worked in every browser just fine!
Is it true that I can only use 4096bit certificates with openfire? I already have a 2048bit wildcard key and it would be annoying if I had to reissue it just for openfire…
This worked great for me thank you!!!