Hello:
I seem to be going round and round trying to sort how to install the certificates as the Openfire SSL guidelines document is a bit dated and seems to be more focused on much earlier versions of the server. I am getting a bit frustrated now.
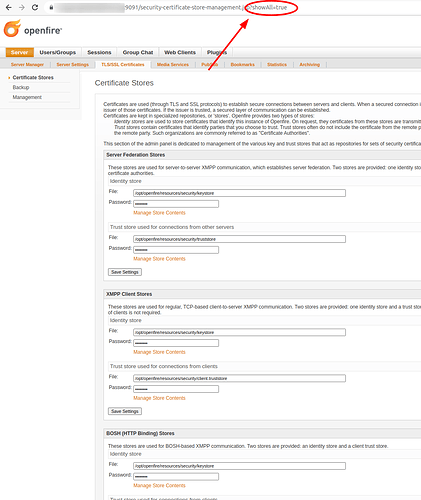
The challenge I have is this: The server runs with the domain name of “chat.ruwg.net” for the XMPP clients and the admin section is running as admin.ruwg.net (on port 9091). I have the “Lets Encrypt” certificate installed for the “chat” ports but I seem to run into errors when I try to install the admin certificate (there are two different certs). Perhaps I am installing them in the wrong place.
I also tried using the certificate management plugin and while I can put the file there (“fullchain.pem”) , it does not seem to get used by the plugin application.
Not to complain about the Openfire application at all as I have been using it for years before it was migrated to a new instance and relocated from one data center to another. In the prior versions, we used first a commercial certificate (GoDaddy) and then we switched Lets Encrypt and that went well. The only suggestion I have is for someone to update the textual information on the admin web page on how to use the stores correctly. It is not that the information may be wrong but rather it would help to explain it differently perhaps.
Thank you.
Kevin Greene