During recent testing of OMEMO in aTalk, one of the device (Device-A) is locked into a state unable to exchange OMEMO messages with Device-B or any other OMEMO devices:
Test environment:
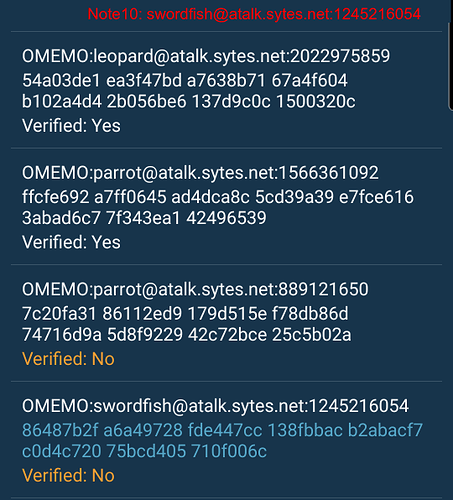
- Device A: Note-10; swordfish@atalk.sytes.net with omemo device ID 2116796881
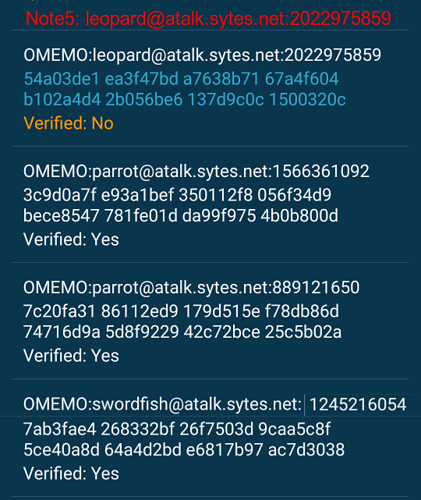
- Device B: Note-5; leopard@atalk.sytes.net with omemo device ID 2022975859
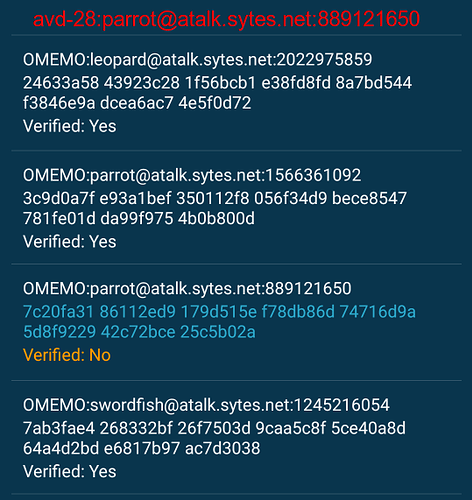
After further investigation on the above two devices, it is found that the SQL database in Device A, actually contains an incorrect fingerprint value for ‘2022975859’ which is different from the correct fingerprint saved in Device-B database. I did not know when and how this situation come about, seems the data corruption was there some time ago.
In aTalk current implementation, I found that there is no defined way for aTalk to break out from this locked state. Neither of the current available options “Regenerate OMEMO Identities” nor “Purge unused Identities” able to resolve the problem. Only the aTalk debug version has a method to completely clear the OMEMO database and rebuild it from scratch able to solve this issue.
With reference to the debug log below: sending a message from Device B to Device A, did indeed trigger an UntrustedOmemoIdentityException. My understanding from the log, OMEMO routine just ignores the message. Not sure if this UntrustedOmemoIdentityException is propagated to the app layer for action.
Any good recommendation how to resolve this locked state in the field.
========== aTalk debug log: OMEMO message sent from Device B to Device A =========
2020-10-29 12:45:11.780 9781-21522/org.atalk.android D/SMACK: SENT (0):
<message to='leopard@atalk.sytes.net' id='1603946711465183634752' type='chat'>
<encrypted xmlns='eu.siacs.conversations.axolotl'>
<header sid='2116796881'>
<key rid='2022975859'>
MwohBf4uNHjhtb0KpcNkO56Vp66XcIu1qZJsOHTu5NsqoroYEAcYASIwZYFJ8hraXNaOMhazgDhcVW+1fYO08lS53ePp3ib9RPyz6pxjO6/Eiqeakvtk7KP02F/Vu63Bj/k=
</key>
<iv>
pF0e6T2kQhPAiabt
</iv>
</header>
<payload>
e5mofCdL4g==
</payload>
</encrypted>
<body>
I sent you an OMEMO encrypted message but your client doesn't seem to support that. Find more information on https://conversations.im/omemo
</body>
<store xmlns='urn:xmpp:hints'/>
<encryption xmlns='urn:xmpp:eme:0' namespace='eu.siacs.conversations.axolotl' name='OMEMO'/>
<request xmlns='urn:xmpp:receipts'/>
<active xmlns='http://jabber.org/protocol/chatstates'/>
<origin-id xmlns='urn:xmpp:sid:0' id='GKRJ-7W46-N6UA-W'/>
</message>
2020-10-29 12:45:12.826 9781-21523/org.atalk.android D/SMACK: RECV (0):
<message xml:lang='en' to='swordfish@atalk.sytes.net/atalk' from='leopard@atalk.sytes.net/atalk' id='E314T-62'>
<encrypted xmlns='eu.siacs.conversations.axolotl'>
<header sid='2022975859'>
<key prekey='true' rid='2116796881'>
MwheEiEFutZSoWNmJJLRIErGii3YZL8XarLoGO+/j+UF0Zlex0kaIQVUoD3h6j9Hvadji3FnpPYEsQKk1CsFa+YTfZwMFQAyDCJSMwohBRnpTs7O8p3Lxib+5SHQtkibdORmco98sx64wYr1MGRyEAAYACIgTnDXtKalHegnQaaW9G0W48d2+/a0GuxBUv9I652wjxcBXKg5m7Ts0ygAMAE=
</key>
<iv>
mqbVvez5yuIk+SVJ
</iv>
</header>
</encrypted>
<origin-id xmlns='urn:xmpp:sid:0' id='4S41-GG51-VTYH-F'/>
</message>
2020-10-29 12:45:12.846 9781-21841/org.atalk.android W/aTalk: [154858] org.jivesoftware.smackx.omemo.OmemoRatchet.retrieveMessageKeyAndAuthTag() Received message from leopard@atalk.sytes.net:2022975859 contained unknown identityKey. Ignore message.
org.jivesoftware.smackx.omemo.exceptions.UntrustedOmemoIdentityException: Untrusted OMEMO Identity encountered:
Fingerprint of trusted key:
24633a58 43923c28 1f56bcb1 e38fd8fd 8a7bd544 f3846e9a dcea6ac7 4e5f0d72
Fingerprint of untrusted key:
54a03de1 ea3f47bd a7638b71 67a4f604 b102a4d4 2b056be6 137d9c0c 1500320c
at org.jivesoftware.smackx.omemo.signal.SignalOmemoRatchet.doubleRatchetDecrypt(SignalOmemoRatchet.java:97)
at org.jivesoftware.smackx.omemo.OmemoRatchet.retrieveMessageKeyAndAuthTag(OmemoRatchet.java:107)
at org.jivesoftware.smackx.omemo.OmemoService.decryptMessage(OmemoService.java:457)
at org.jivesoftware.smackx.omemo.OmemoService.onOmemoMessageStanzaReceived(OmemoService.java:1192)
at org.jivesoftware.smackx.omemo.OmemoManager$3.run(OmemoManager.java:959)
at java.lang.Thread.run(Thread.java:919)
2020-10-29 12:45:12.850 9781-21841/org.atalk.android W/aTalk: [154858] org.jivesoftware.smackx.omemo.OmemoService.onOmemoMessageStanzaReceived() Could not decrypt incoming message:
org.jivesoftware.smackx.omemo.exceptions.CryptoFailedException: Transported key could not be decrypted, since no suitable message key was provided. Provides keys: [2116796881]
at org.jivesoftware.smackx.omemo.OmemoRatchet.retrieveMessageKeyAndAuthTag(OmemoRatchet.java:127)
at org.jivesoftware.smackx.omemo.OmemoService.decryptMessage(OmemoService.java:457)
at org.jivesoftware.smackx.omemo.OmemoService.onOmemoMessageStanzaReceived(OmemoService.java:1192)
at org.jivesoftware.smackx.omemo.OmemoManager$3.run(OmemoManager.java:959)
at java.lang.Thread.run(Thread.java:919)