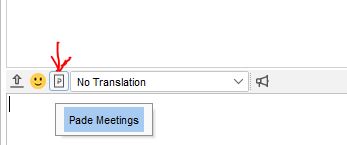
Spark Pade Meetings Plugin 0.0.8 by Dele Olajide generates incorrect url when the button is clicked.
For example, server name is openfire.domain.local
Generated link is like this: https://domain.local:7443/ofmeet/user-1620918133346
But there must be https://openfire.domain.local:7443/ofmeet/user-1620918133346
Video conferencing web client button opens the correct site address
How can i fix this button?
Are you using openfire.domain.local as domain name on login screen in Spark?
Yes, openfire.domain.local as domain.
Plain authentication and LDAP+SSO GSSAPI - same problem on Spark 2.9.4 and Spark 3.0.0-beta
When i try this on my test server, which is only a test server and both Openfire and Spark are on the same machine, no LDAP or SSO, it seems to work ok. My server is ‘wroot’ and when i press Pade button it generates https://wroot:7443 URL and opens Pade window. Maybe this is a configuration thing. @Dele_Olajide ?
Just to make sure, you say you use openfire.domain.local to login in Spark. But is your xmpp domain name the same on the first page in Admin Console?
FQDN is openfire.domain.local and xmpp.domain is domain.local.
After I changed the value of xmpp.domain to openfire.domain.local the authorization broke, the admin panel no longer authorizes me and Spark too
It is not recommended to change your xmpp.domain like that. It will break things. To change your xmpp domain you will have to go through setup process again. Which you can try by changing setup tag in openfire.xml to the opposite one. Of course, first backups.
Superb, it worked! Thank you!
Pade by default uses the server name. It however possible to override that with a properties file created in the USER_HOME\Spark folder called ofmeet.properties.
Create a single entry for the property url. On my Windows PC that would be
C:\Users\dele\AppData\Roaming\Spark\ofmeet.properties
url=https://openfire.domain.local:7443/ofmeet/
Are Jitsi authorization logs written somewhere?
Can i use fail2ban or ip-tables with Jitsi to protect against password guessing, like this Enable fail2ban to monitor openfire login logs ?
I found a debug.log, I will try to configure fail2ban